The Firewall-as-a-Service (FWaaS) plug-in adds perimeter firewall management to OpenStack Networking (neutron). FWaaS uses iptables to apply firewall policy to all virtual routers within a project, and supports one firewall policy and logical firewall instance per project.
FWaaS operates at the perimeter by filtering traffic at the OpenStack Networking (neutron) router. This distinguishes it from security groups, which operate at the instance level.
NOTE
FWaaS is currently in technical preview; untested operation is not recommended.
The example diagram below illustrates the flow of ingress and egress traffic for the VM2 instance:
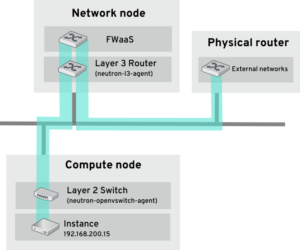
Figure 1. FWaaS architecture
I-Enable FWaaS
- Install the FWaaS packages:
# yum install openstack-neutron-fwaas python-neutron-fwaas
- Enable the FWaaS plugin in the neutron.conffile:
service_plugins = neutron.services.firewall.fwaas_plugin.FirewallPlugin
- Configure FWaaS in the fwaas_driver.inifile:
[fwaas] driver = neutron.services.firewall.drivers.linux.iptables_fwaas.IptablesFwaasDriver enabled = True [service_providers] service_provider = LOADBALANCER:Haproxy:neutron_lbaas.services.loadbalancer.drivers.haproxy.plugin_driver.HaproxyOnHostPluginDriver:default
- FWaaS management options are available in OpenStack dashboard. Enable this option in the local_settings.pyfile, usually located on the Controller node:
/usr/share/openstack-dashboard/openstack_dashboard/local/local_settings.py 'enable_firewall' = True
- Restart neutron-serverto apply the changes.
# systemctl restart neutron-server
II-Configure FWaaS
First create the firewall rules and create a policy to contain them, then create a firewall and apply the policy:
- Create a firewall rule:
$ neutron firewall-rule-create --protocol <tcp|udp|icmp|any> --destination-port <port-range> --action <allow|deny>
The CLI requires a protocol value; if the rule is protocol agnostic, the any value can be used.
- Create a firewall policy:
$ neutron firewall-policy-create --firewall-rules "<firewall-rule IDs or names separated by space>" myfirewallpolicy
The order of the rules specified above is important. You can create an empty firewall policy and add rules later, either with the update operation (when adding multiple rules) or with the insert-rule operations (when adding a single rule).
Note: FWaaS always adds a default deny all rule at the lowest precedence of each policy. Consequently, a firewall policy with no rules blocks all traffic by default.
III-Create a firewall
$ neutron firewall-create <firewall-policy-uuid>
The firewall remains in PENDING_CREATE state until an OpenStack Networking router is created, and an interface is attached.
IV-Allowed-address-pairs
Allowed-address-pairs allow you to specify mac_address/ip_address (CIDR) pairs that pass through a port regardless of subnet. This enables the use of protocols such as VRRP, which floats an IP address between two instances to enable fast data plane failover.
NOTE
The allowed-address-pairs extension is currently only supported by these plug-ins: ML2, Open vSwitch, and VMware NSX.
- Basic allowed-address-pairs operations
Create a port with a specific allowed-address-pairs:
# neutron port-create net1 --allowed-address-pairs type=dict list=true mac_address=<mac_address>,ip_address=<ip_cidr>
- Adding allowed-address-pairs
# neutron port-update <port-uuid> --allowed-address-pairs type=dict list=true mac_address=<mac_address>,ip_address=<ip_cidr>
NOTE
OpenStack Networking prevents setting an allowed-address-pair that matches the mac_address and ip_address of a port. This is because such a setting would have no effect since traffic matching the mac_address and ip_address is already allowed to pass through the port.